Security Posture stories - Page 3

Adaptiva launches Aida AI adviser for endpoint teams
Last month
#
data protection
#
endpoint protection
#
it automation
Adaptiva debuts Aida AI adviser to help IT and security teams query vast endpoint estates in plain English and speed up exposure management.

Vorlon survey finds SaaS AI security gaps among CISOs
Last month
#
data protection
#
cloud security
#
application security
Vorlon survey reveals nearly all CISOs suffered SaaS and AI security incidents in 2025, despite high confidence in existing controls.

Nudge Security adds AI agent discovery for workplace risk
Last month
#
data protection
#
digital transformation
#
cloud security
Nudge Security has launched AI agent discovery to help firms spot risky employee-built agents, tighten access and curb shadow AI sprawl.

Horizon3.ai revenue doubles as NodeZero demand surges
Last month
#
devops
#
cloud security
#
application security
Horizon3.ai doubles ARR as more than 5,200 organisations adopt its NodeZero platform, fuelled by MSSP demand and rising cyber risks.

Qualys launches Agent Val to prove exploitable risks
Last month
#
socs
#
cybersecurity
#
agentic ai
Qualys debuts Agent Val to validate real exploit paths in live systems, promising sharply reduced noise and faster remediation for teams.

NSS Labs backs AI guardrail tests amid security fears
Last month
#
firewalls
#
devops
#
digital transformation
NSS Labs warns many enterprise AI guardrails fail basic security tests, urging independent, real-world validation of protections.

Red Hat survey finds cloud security incidents rife
Last month
#
data protection
#
digital transformation
#
cloud security
Red Hat survey finds 97% of organisations hit by cloud-native security incidents, forcing delays, higher costs and loss of customer trust.

Akamai adds AI tools to speed Zero Trust segmentation
Last month
#
virtualisation
#
firewalls
#
ransomware
Akamai injects new AI into Guardicore Segmentation to automate Zero Trust policies, curb lateral movement and shrink breach blast radius.

BeyondTrust warns of 467% rise in enterprise AI agents
Last month
#
crm
#
hyperscale
#
pam
BeyondTrust warns a surge of unsupervised AI agents is creating a hidden “shadow workforce” with admin-level access inside enterprises.

Saviynt launches AI agent identity security platform
Last month
#
digital transformation
#
pam
#
cloud security
Saviynt unveils an AI identity security platform to govern autonomous agents across major enterprise AI stacks and close emerging access gaps.

ExtraHop launches AI network visibility & governance tool
Last month
#
firewalls
#
data protection
#
hybrid cloud
ExtraHop unveils an AI network visibility tool to track agents, expose shadow AI and tighten security and governance across enterprise systems.

CyberProof launches Reveal360 for unified security view
Last month
#
hybrid cloud
#
digital transformation
#
cloud security
CyberProof unveils Reveal360, a role-based platform unifying threat, defence and asset data to give enterprises a single security view.

Tanium adds AI tools across security & endpoint management
Last month
#
hybrid cloud
#
digital transformation
#
cloud security
Tanium rolls out AI-driven tools to tighten endpoint governance, speed incident response and unify security, exposure and device management.

N-able sees network attacks surge as AI boosts SOCs
Last month
#
firewalls
#
network security
#
cloud security
Network and perimeter attacks are resurging as SOCs lean on AI and SOAR, with 90% of investigations now handled autonomously.

Red Hat finds cloud security incidents hit 97% of firms
Last month
#
data protection
#
hybrid cloud
#
cloud security
Red Hat reports 97% of organisations suffered cloud-native security incidents last year, exposing basic failings in configuration and governance.
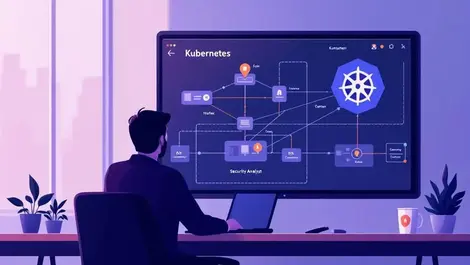
Zero Networks launches Kubernetes Access Matrix tool
Last month
#
virtualisation
#
devops
#
cloud security
Zero Networks has unveiled Kubernetes Access Matrix, a visual tool mapping cluster traffic to help teams curb lateral movement and policy sprawl.

BeyondTrust expands Pathfinder to secure AI agents
Last month
#
endpoint protection
#
digital transformation
#
pam
BeyondTrust expands Pathfinder to discover, govern and lock down proliferating enterprise AI agents, identities, privileges and secrets.

GitLab widens AI access & sets flat review pricing
Last month
#
devops
#
application security
#
devsecops
GitLab opens agentic AI to free-tier users, sets USD $0.25 flat fee for automated code reviews and expands security false-positive filtering.

Bedrock expands ArgusAI for AI agent risk oversight
Last month
#
data protection
#
hyperscale
#
cloud security
Bedrock expands ArgusAI to map AI agents, MCP servers and Snowflake Cortex access, promising unified oversight of enterprise AI risk.
Delinea warns AI adoption is widening identity gaps
Last month
#
data protection
#
digital transformation
#
pam
Delinea warns that rapid AI rollout is eroding identity controls, leaving machine accounts exposed and widening security blind spots.